Introducing WAIRZ an AI Assisted Firmware Analysis Tool
Over the last year I've quietly been working on an exciting project! One that brings together my favourite open source IoT and reverse engineering tools, combines them in one package and gives the AI client of your choice access to them through a robust MCP server.
The tool is called Wairz, a play on firmware, AI and one of my favourite video games Skyrim. It's entirely open source and of course free.

You can get all the details at the official wairz.ai docs page.
On the surface Wairz looks similar to other firmware vulnerability scanners. You upload firmware and the back-end uses various tools to extract out the components, perform static analysis for component and version identification, checks binaries and libraries for weak configuration issues for example stack canaries not enabled. You can also search the identified components in the generated SBOM against the public NVD database to compile a list of known vulnerabilities.
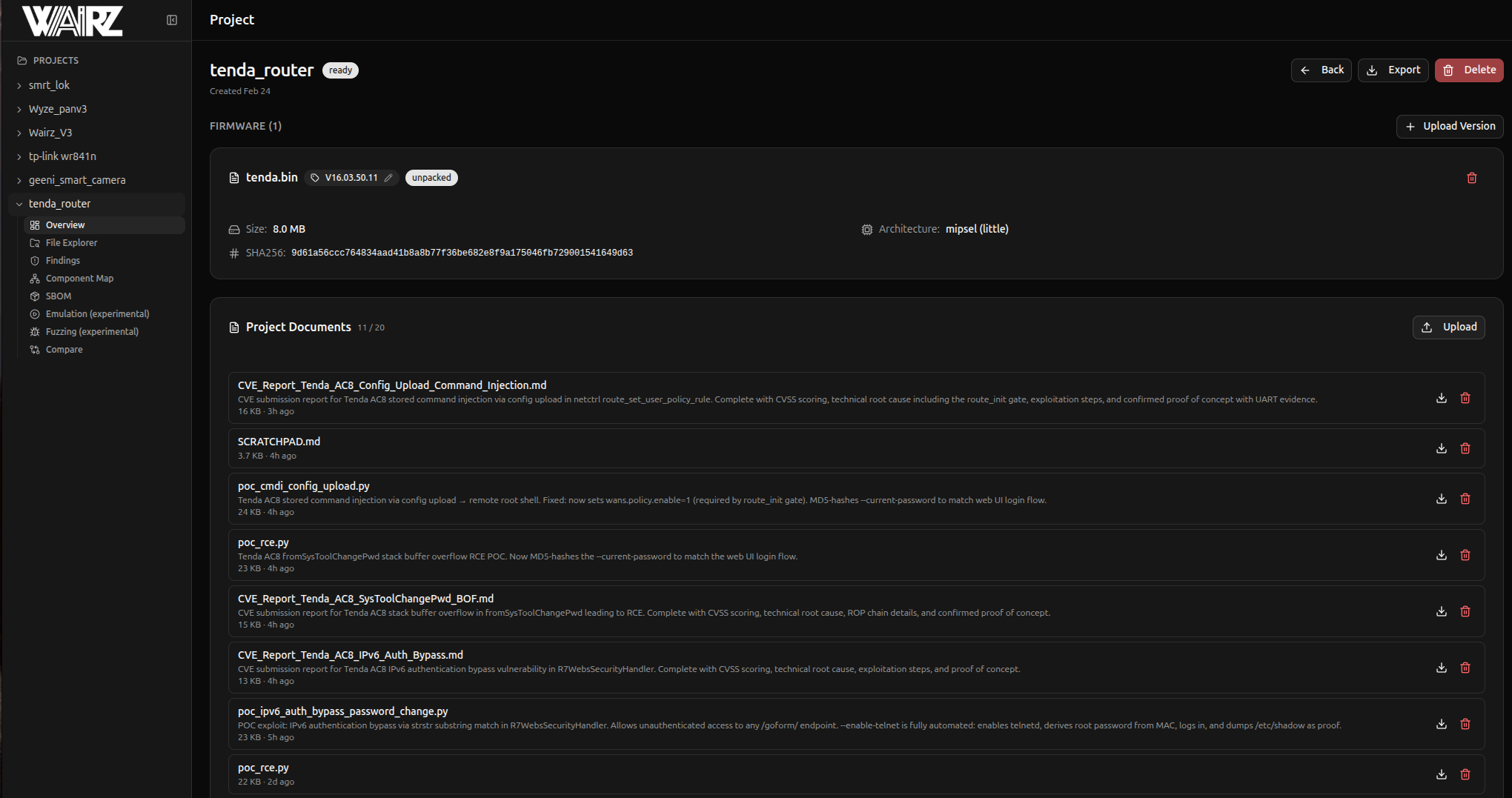
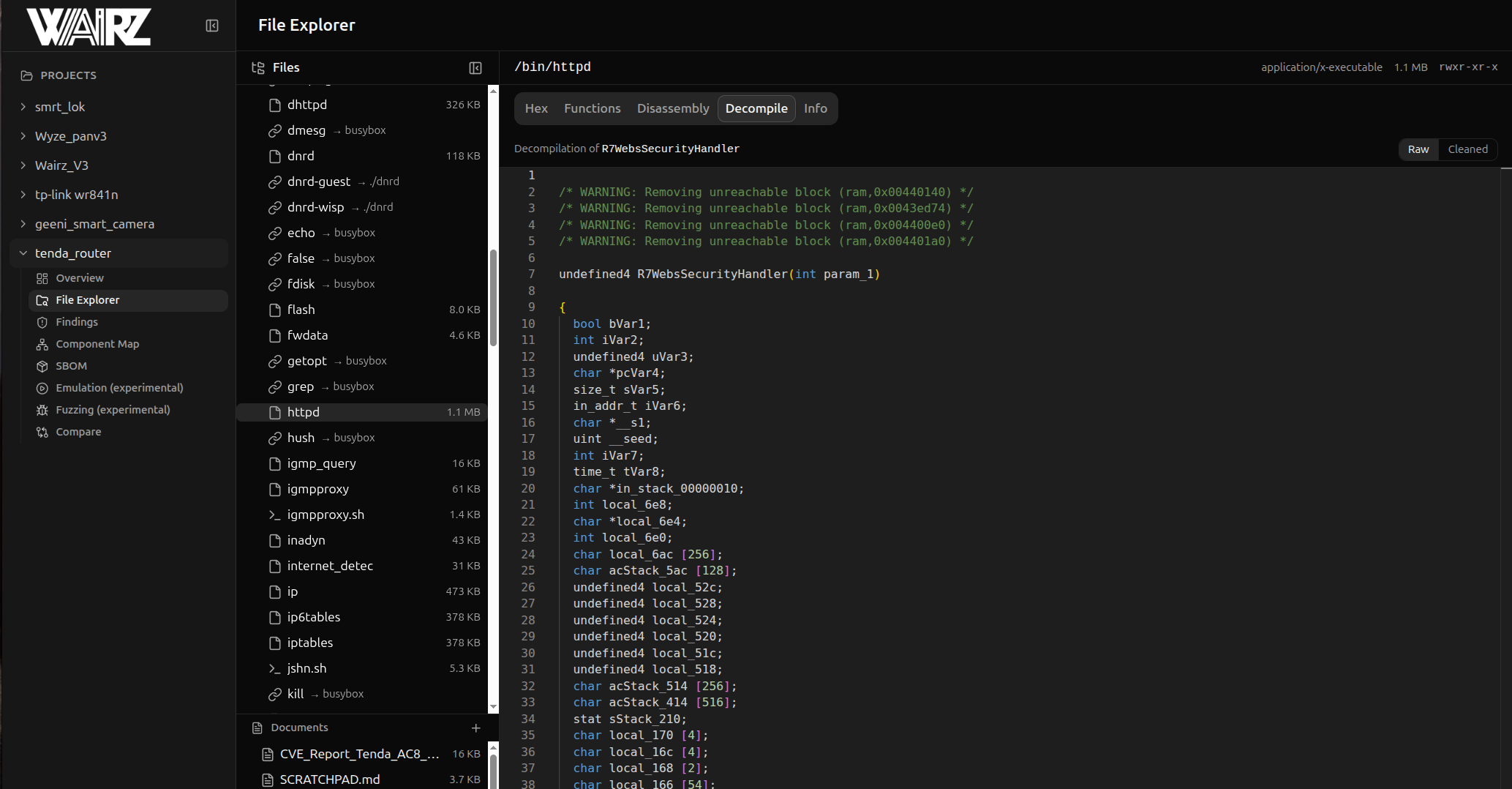
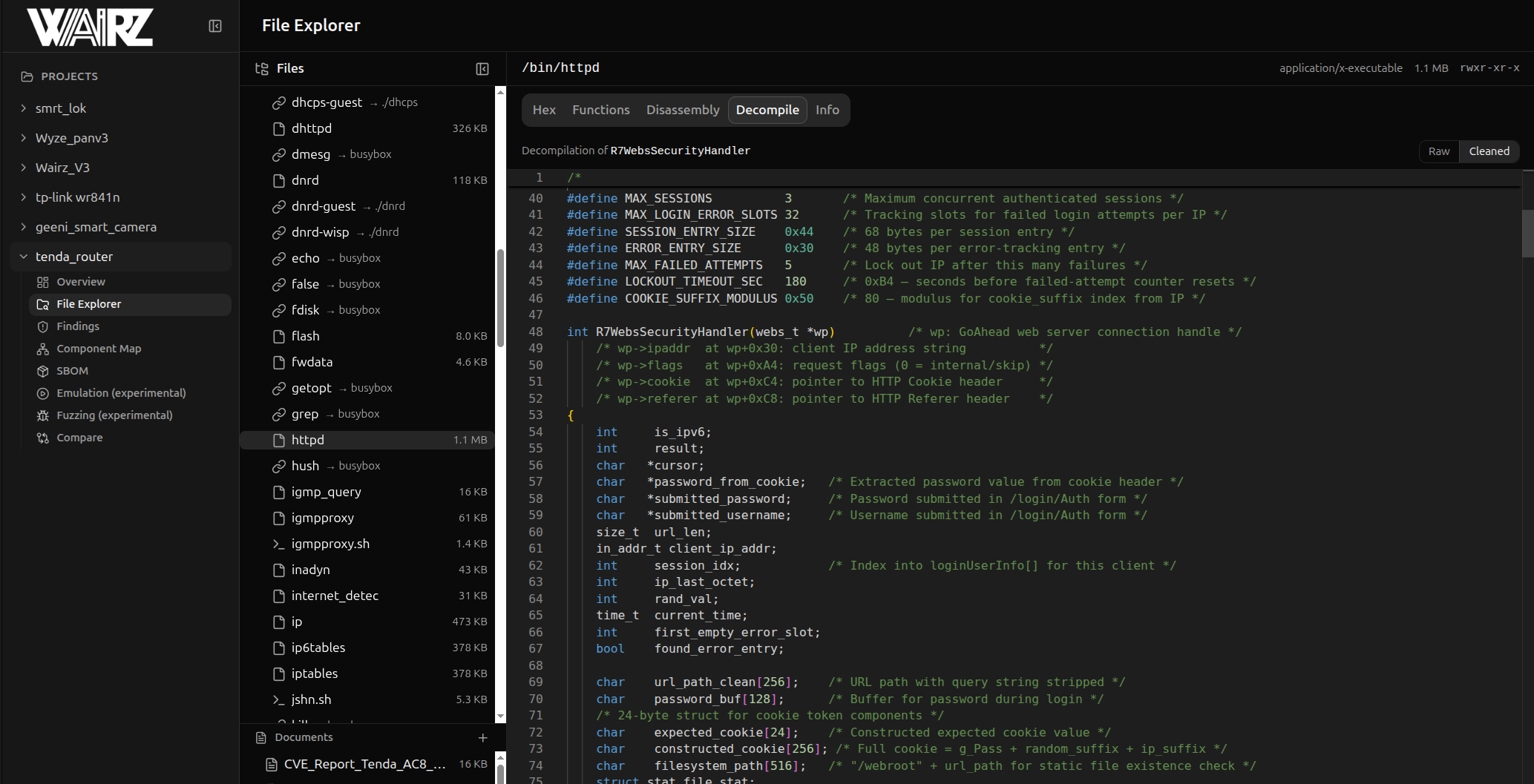
I also added in some cool features that I always wanted to see in these style of firmware vuln scanners. The first feature is that while exploring the file tree, not only can you view plain-text files like config or .sh scripts, if the file is a binary you can view the raw-hex, look at the disassembly of it, and even a decompiled viewed powered by Ghidra.
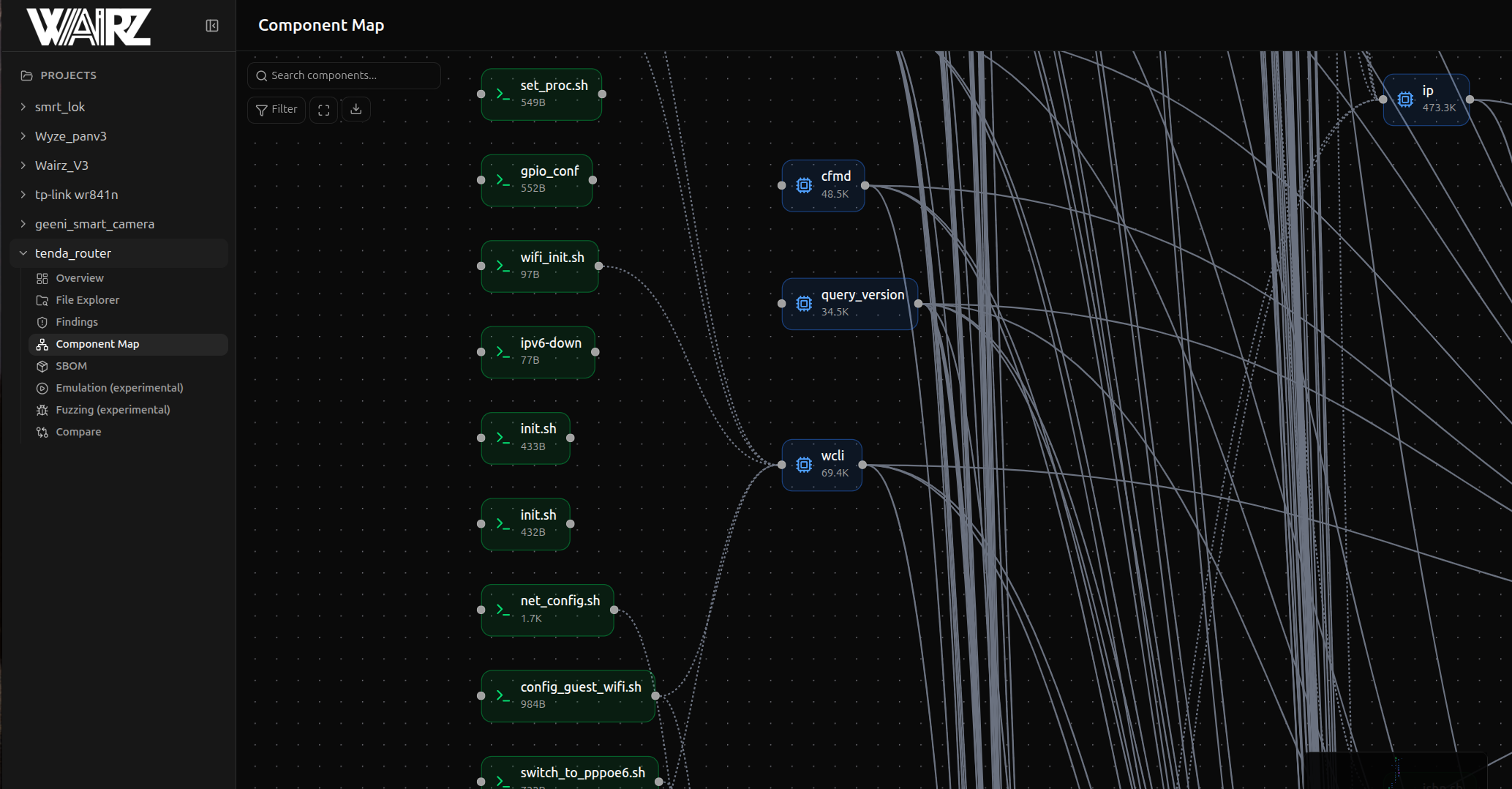
The second cool feature is a component map that shows how different pieces of the firmware interact with each other, for example if a binary is called from an init script and imports multiple libraries you can see their relations and the paths between them. This really helps with reverse engineering and taint analysis.
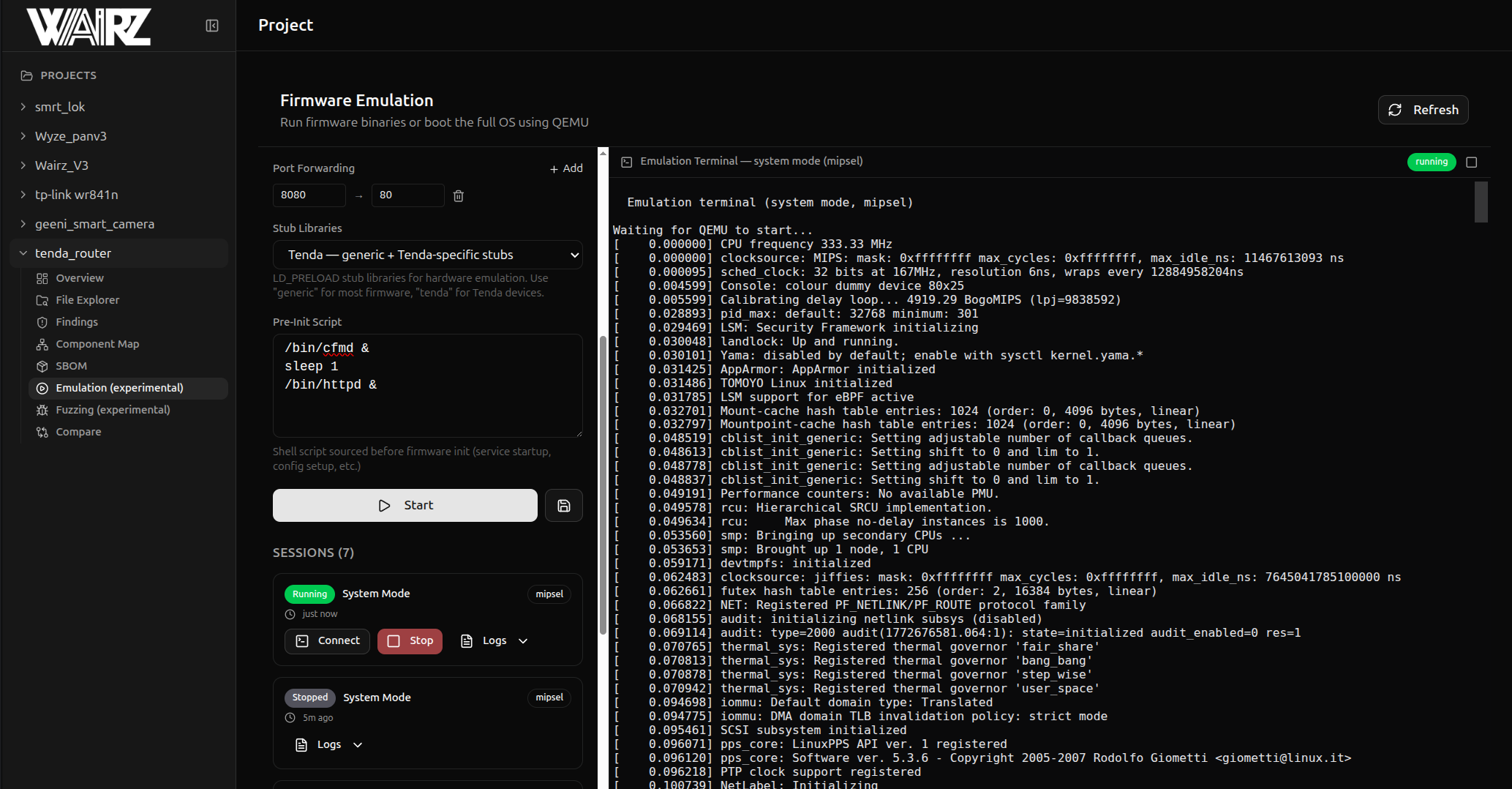
In addition to all of these static analysis tools I also added in the ability to perform user mode and full system mode emulation of firmware. This allows you access to easily test and debug the firmware and any potential findings. Finally, you can conduct fuzzing campaigns via AFL++ directly from Wairz which integrates with the built in emulation.
Wairz has two launch options, one of which where everything runs contained in a docker environment with multiple docker containers. This provides a few benefits, firstly all of the tools, dependencies and that jazz are all already installed and configured for you. The second big one is that it provides a level of sandboxing. This is important since you're dealing with potentially untrusted firmware samples that have root file systems which closely mimic the root file system on the Linux system you'd probably run it from. I've totally never accidentally done cd /etc instead of cd etc and ended up lost in my own systems configs...
But then we add AI
Which I promise you'll actually like and isn't forced slop
All of the above combined with a nice GUI already makes Wairz a great tool that's fun to use (in my humble opinion), however, it's real power comes from the MCP server and its ability to turn tools like Claude Code, Codex or Cursor into absolute monsters at reverse engineering and finding vulns in firmware.
The MCP server has over 60 tools (which you can see the full docs on here https://wairz.ai/mcp-tools/) some of which include reverse engineering, taint analysis, strings extraction, connecting to live devices via UART and even setting up and running emulation or fuzzing. Essentially, anything you can do manually the AI can as well. Combining these tools with the instructions and prompting that Wairz provides behind the scenes along with the ability to add custom instructions and a human in the loop equals a very capable firmware reverse engineering tool.
Due to the MCP server integration you can dictate how much or how little AI assistance you get. For example you can set the AI on a fully autonomous end-end security assessment where you don't provide any further input, or ask it very directed questions about specific functions, files, lines of code or really anything you see in the firmware. One AI assistance feature I find very useful is the ability to get AI to clean up the output from Ghidra into even more human readable C. It does this by renaming variables and functions to names that make sense and adding in comments about what is being done.
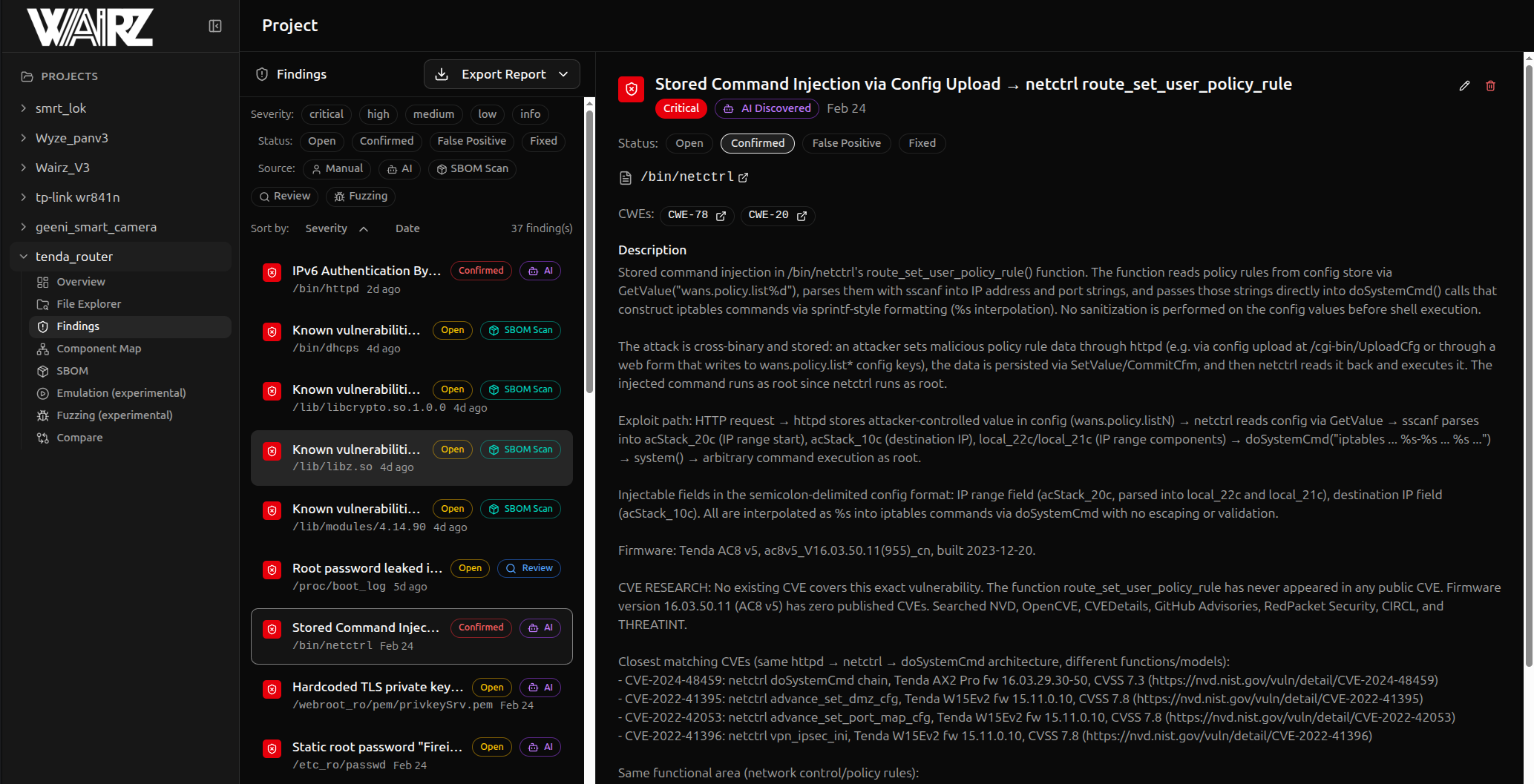
Curious if Wairz works before taking it for a spin, here are a few critical vulns and POCs that Wairz found and created.
These are some of the ones I'm comfortable sharing at this point because they're in the LAN only side of a Tenda router. Unfortunately Tenda has no responsible disclosure program or even a security contact and are well known to not respond to security researchers so I've published the details and submitted the reports for CVEs.
Happy (AI Assisted) Hacking - DigitalAndrew
